Service Overview
At eRexa, we deliver comprehensive Hardware Services designed to equip businesses with the reliable, high-performance technology they need to operate efficiently and securely. From hardware supply and installation to lifecycle management and technical support, we provide complete solutions that ensure your IT environment runs seamlessly.

Hardware Procurement & Supply
We partner with leading global manufacturers to provide a wide range of IT hardware — including servers, networking equipment, storage devices, workstations, and peripherals. Our procurement team ensures that every product meets performance, compatibility, and scalability requirements tailored to each client’s needs.
Installation & Configuration
Our certified engineers handle the full deployment process — from hardware setup and system configuration to network integration and testing. We ensure all components are optimized for performance and reliability within your existing IT infrastructure.

3. Maintenance & Support
eRexa provides ongoing hardware maintenance, troubleshooting, and repair services to minimize downtime and maximize operational continuity. Through preventive maintenance and timely upgrades, we help businesses extend the lifespan and efficiency of their IT assets.
Asset Management & Lifecycle Services
We assist clients in managing their hardware assets throughout their lifecycle — from acquisition and deployment to decommissioning and disposal. Our structured approach ensures compliance with data security standards and supports sustainable, cost-effective hardware management.


Vendor Partnerships
Through our partnerships with global technology leaders such as Cisco, Fortinet, Dell, HP, and Lenovo, we deliver certified hardware solutions backed by manufacturer warranties and professional after-sales support.
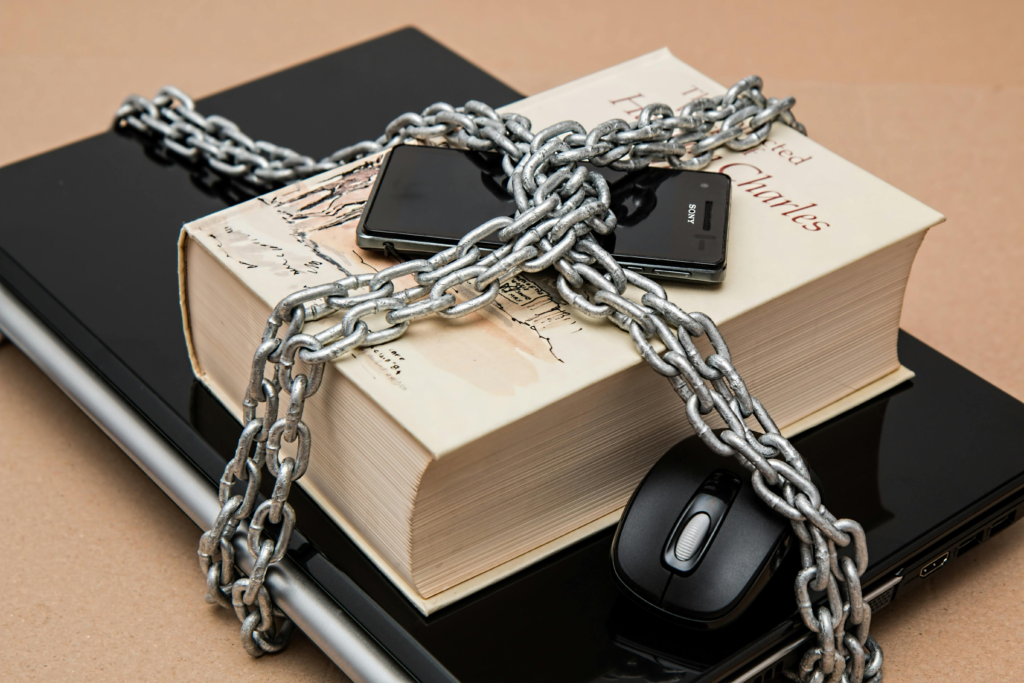
IT Security & Resilience
Security is at the heart of everything we do. Our security services include firewalls, endpoint protection, intrusion detection, and disaster recovery planning. We help organizations safeguard their data, mitigate risks, and maintain compliance with global cybersecurity standards.